Executive Summary
You know your policy library has gaps. You just don’t know which ones matter most, or how to find them in a timeframe your team can actually afford.
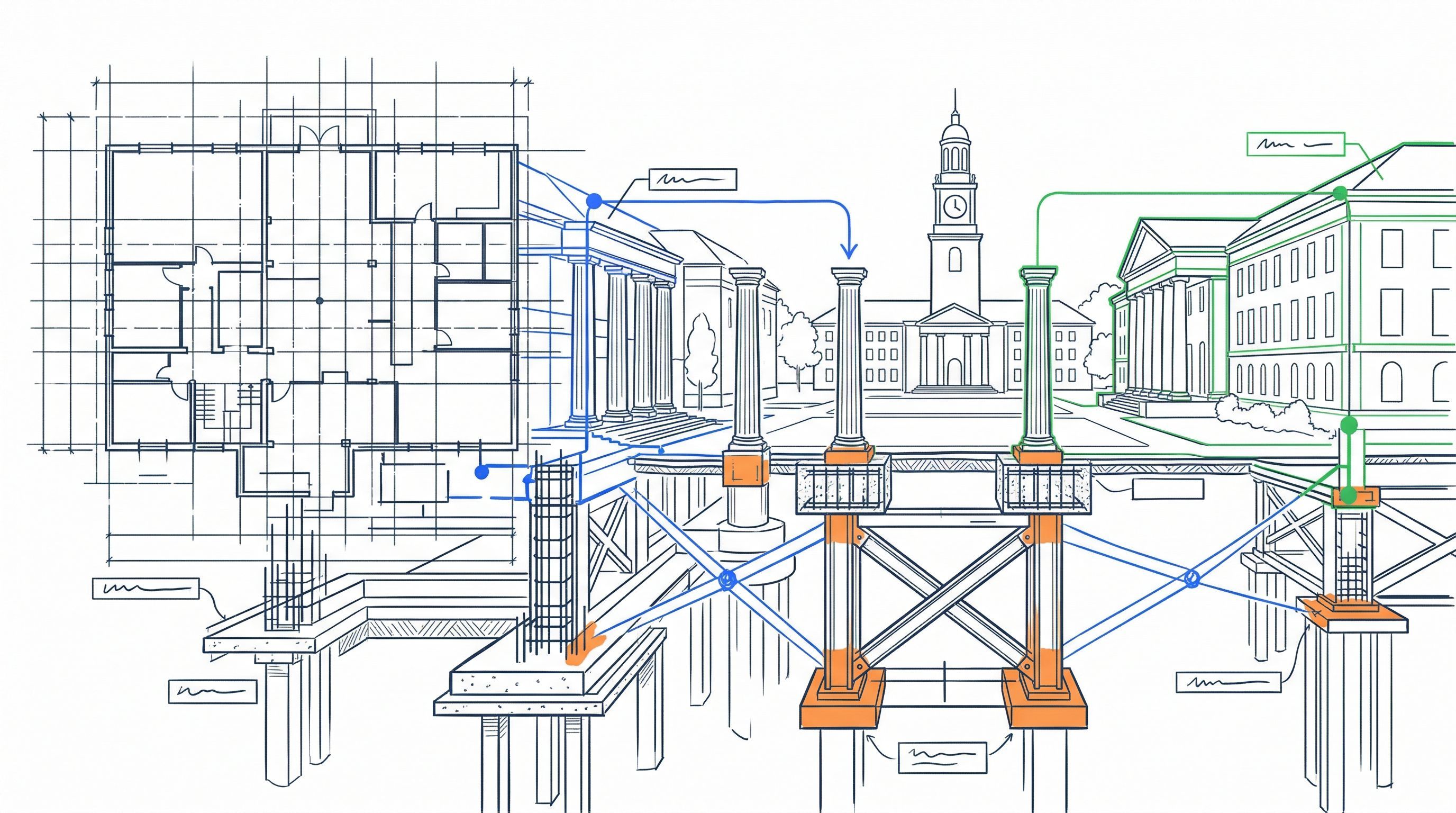
Higher education IT policy isn’t a documentation problem. It’s a governance problem. Most institutions maintain written policies. But the distance between what should be documented and what exists creates what this guide calls Governance Debt. Like deferred maintenance on a building, it follows predictable patterns and compounds over time. Regulations change, threats evolve, and higher education best practices shift each year, while the documentation stays where it was when someone last had time to update it.
This guide shows you how to measure your Governance Debt and pay it down, not through a one-time renovation project but through an annual cycle your team can actually sustain.
How this guide came together. Over years of advisory work with higher education CIOs and CISOs, we kept seeing the same patterns. Some institutions had well-documented authentication programs but nothing written down for ransomware response. Others had critical technical practices that existed entirely in senior staff members’ heads. We started tracking the patterns as reference material for our own engagements. That reference material evolved into the CampusCISO IT Policy Framework. The 2026 edition reflects analysis of 410 institutional policy libraries across every Carnegie tier, including every R1 research university in the United States.
Three core patterns emerged from the institutions we reviewed:
- The Authentication Floor. Identity management is the one area of consensus. We found documented password and access-control practice at over 80% of institutions at every tier, and password standards at 100% of large research universities.
- The Ransomware Cliff. Attack volumes against education have nearly doubled in recent years. But we found documented ransomware response procedures at only 57% of large research universities and just 2% of small baccalaureate institutions.
- The Oral Tradition Liability. Critical technical practices live in people’s heads instead of written standards. Documented standards fall from 76% at the largest research universities to 37% at small institutions. Not having documented standards creates a risk that when staff leave, the institution’s security program leaves with them.
We defined a framework of 17 policies and 24 standards that reflect what higher education institutions actually do. This was based on observed data from 410 institutions, not what a generic framework prescribes.
What you’ll know how to do after reading this:
- Identify which policy gaps at your institution create real exposure
- Map your regulatory obligations to the policies and standards that support them, including the overlapping requirements that trip up many IT leaders
- Conduct either a high-level self-assessment in about 20 staff hours or a more thorough roadmap exercise in about 70 to 130 hours
- Establish an annual review and refresh program that fits your team’s actual capacity, with a defensible framework to prioritize what to tackle first and what can wait
The goal isn’t to fix everything at once. It’s to establish the annual cadence that keeps your Governance Debt from compounding.
Who this guide is for: CIOs, CISOs, IT leadership, and governance committees at higher education institutions of any size. While the regulatory examples are US-specific, you can apply the structural principles to institutions in any jurisdiction.