5 OWASP MIA (Missing in Action)
This section has the following chapters:
- ‘Using the HTML5 Fullscreen API for Phishing Attacks’, OWASP MIA and ‘We need SAST technology for browsing the web safely’
- Big Security Challenges with Creating APIs for US Gov Agencies
- Example example of SQL Injection using Database.SQLQuery from GitHub
- Guidelines of Owasp
- Hack Yourself First Jeremiah at TEDxMaui
- I think the time as come for OWASP to have its own secure browser
- Nice list of 20 online coding tools
- No OWASP app on the OSX AppStore (Nov 2013)
- OWASP and Privacy issues, we need to be involved
- Software Labels - Jeff’s OWASP AppSecDC 2010 presentation (another dropped good idea)
5.1 ‘Using the HTML5 Fullscreen API for Phishing Attacks’, OWASP MIA and ‘We need SAST technology for browsing the web safely’
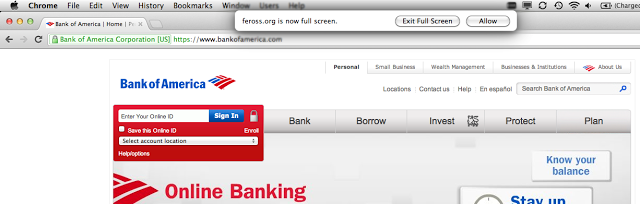
Really nice article from Feross Aboukhadijeh on the Phishing potential of HTML5 FullScreen features:
You can read it at Using the HTML5 Fullscreen API for Phishing Attacks
Note that on Chrome in OSx it will show this alert
… if you’re not in Full Screen already. But in a lot of cases that will be easy to dismiss (specially with users used to click that ‘Allow’ button). See note below on using SAST technology to deal with this.
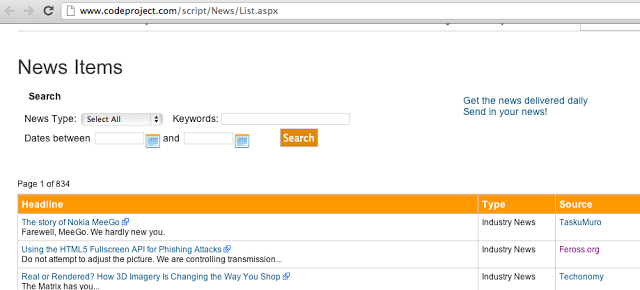
What is interesting about this story is that is also shows how developers DO care about security. There is a thread about it on Hackers News and on Reddit and I found this article via the CodeProject’s Daily New email:
OWASP MIA
But where’s OWASP on this thread?
- both Hackers News and on Reddit have no mention for OWASP (just search the page)
- Feross article also has no mention of OWASP
- A quick search for Feross’ name and OWASP didn’t show anything
- Nothing on OWASP’s website (which means that he has not presented at an OWASP conference or chapter)
So is Feross involved at all with OWASP? I can’t find it.
As one of the guys who created one of the best ClickJacking examples HOW TO: Spy on the Webcams of Your Website Visitors (and only 22 years old), he is clearly part of the new generation of AppSec Security experts.
But if OWASP is not able to attract him and create environments / ecosystems for Feross (and other new stars), that means that we (OWASP) are starting to be irrelevant for the new Generation :(
And that is a fundamental problem with OWASP. We should be measuring OWASP’s success by its community and relevance. But it is much harder to measure ‘What could had happened’ than ‘what is happening’. This (amongst others) is why I proposed a new model for OWASP so that OWASP can reinvent itself and find ways to add value to Feross (and its community).
**
****We need SAST technology for browsing the web safely**
So how to do solve this? Unless we start to have SAST-like Technology on browsers (which allow us to write context-sensitive rules that know the difference between YouTube and Feross’ website) I don’t think we will find a good solution (it’s just patches and hacks)
5.2 Big Security challenges with creating APIs for US Gov agencies
So Barack Obama Directs All Federal Agencies to Have an API
Here is the White house memo (pdf) which mandates the implementation of “Digital Government: Building a 21st Century Platform to Better Serve the American People” (pdf).
The good news it that at least security and privacy seems to be taken into account (with it’s own chapter and focus)
I haven’t read the document but after a skim, it looks like there is more focus on the non-secure-application-development ‘security side’ of these APIs.
And this could be an issue, since creating APIs is usually done by exposing internal systems or WebServices, which will now need to have much higher level of security than before (when they were connected to much less hostile environment).
I also like the use/focus on Privacy, since that will be a good way to drive coding and application changes.
This is a great opportunity for OWASP community to be involved since there is going to be a lot of API developers out there that could do with some help
5.3 Example example of SQL Injection using Database.SQLQuery from GitHub (and idea for Cat.NET workflow)
After posting Another example why SATS technology needs custom rules (re: Detecting SQL Injection on .NET Entity framework) I did this search on GitHub, and found an example of that dangerous Database.SqlQuery API in use:
- https://github.com/caioketo/QIERP/blob/master/QIERPDatabase/VerpContext.cs#L55
- with default sa pwd: https://github.com/caioketo/QIERP/blob/master/QIERPDatabase/VerpContext.cs#L18
- use of Database.ExecuteSqlCommand: https://github.com/caioketo/QIERP/blob/master/QIERPDatabase/VerpContext.cs#L59
These one allows callers to create SQL Injection (which means that whoever is consuming those APIs need to be VERY careful)
- https://github.com/revolutionaryarts/wewillgather/blob/master/src/Libraries/Gather.Data/GatherObjectContext.cs#L69
- https://github.com/philpeace/PointyPointy/blob/master/PointyPointy.Web/Data/StoryContext.cs#L51
- https://github.com/samandmoore/GetRDoneWeb/blob/master/GetRDone/GetRDoneContext.cs#L25
- https://github.com/slask/MVCArchitectureTemplate/blob/master/Solution/DataAccess/Context/ScrabbleClubContext.cs#L106
This one look OK (on diagonal reading)
- https://github.com/JayBeavers/ChronoZoom/blob/exceptionalIo/Source/Chronozoom.Entities/Storage.cs#L122 (Ok, because timelinesMap.Keys are GUIDs). There are multiple other uses of Database.SqlQuery which look ok because either the parameters options were used, or the string concats where done on GUIDs)
Idea for Cat.NET workflow
Now wouldn’t it be great if we could automate an Cat.NET (or another SAST scanner) to do this type of analysis automatically?
For example an Bot ot TeamCity workflow that:
- cloned/pulled a repo
- compile it
- run cat.net on it (with default or custom rules)
- automatically package the issues discovered
- send issues to repo owner
- allow rules to be customised (maybe as an XML file somewhere in the repo), for example, wrappers around Database.SQLQuery need to be marked as sinks)
- go back to 1
I also would like a mode to create UnitTests based on the vulns discovered (using SAST and DAST techniques), but that is a topic for another post :)
Ideally all this would be linked to Developer friendly guidance (like TeamMentor or OWASP content) in order to help the developers to easily understand the issues and write the required fixes
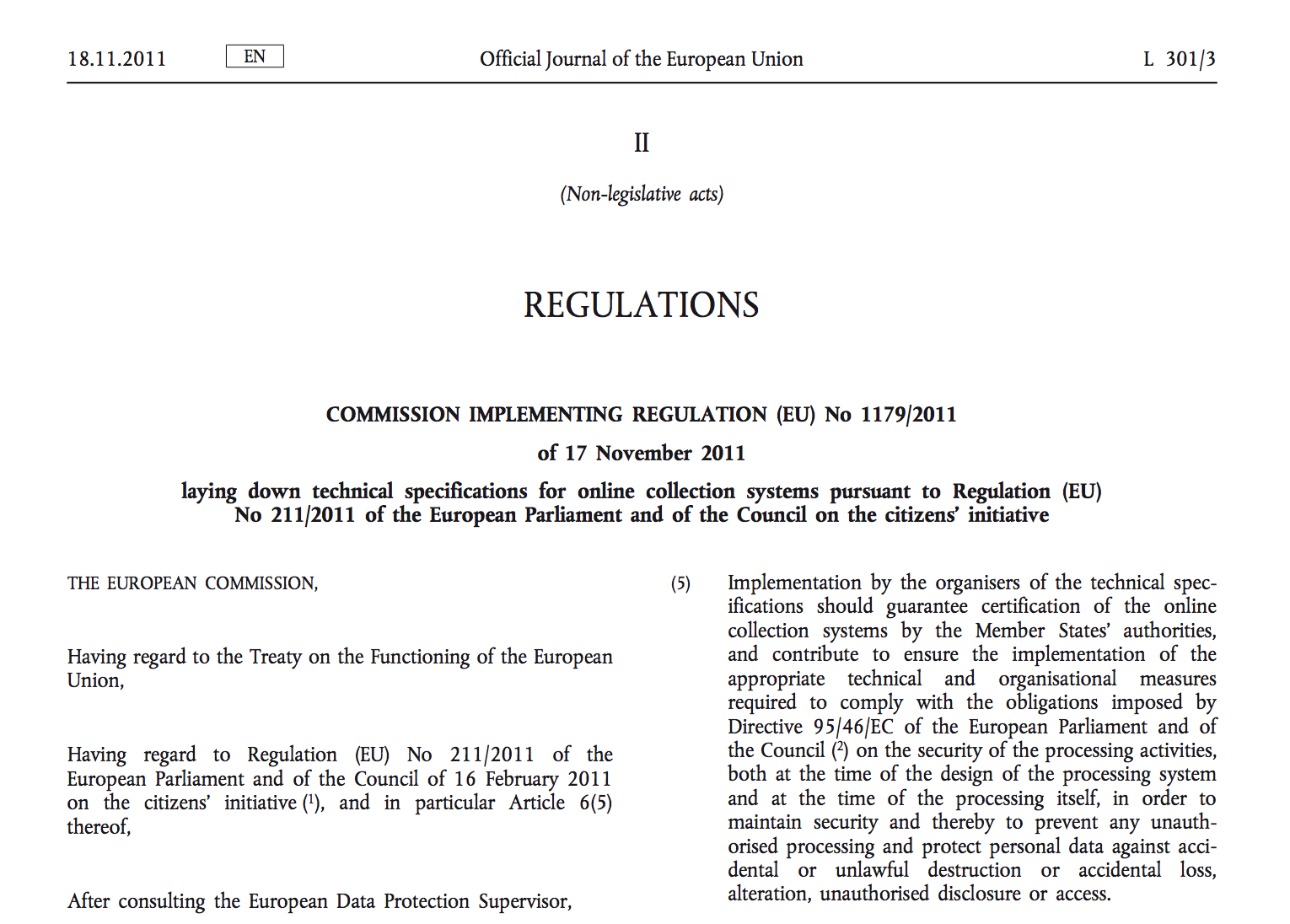
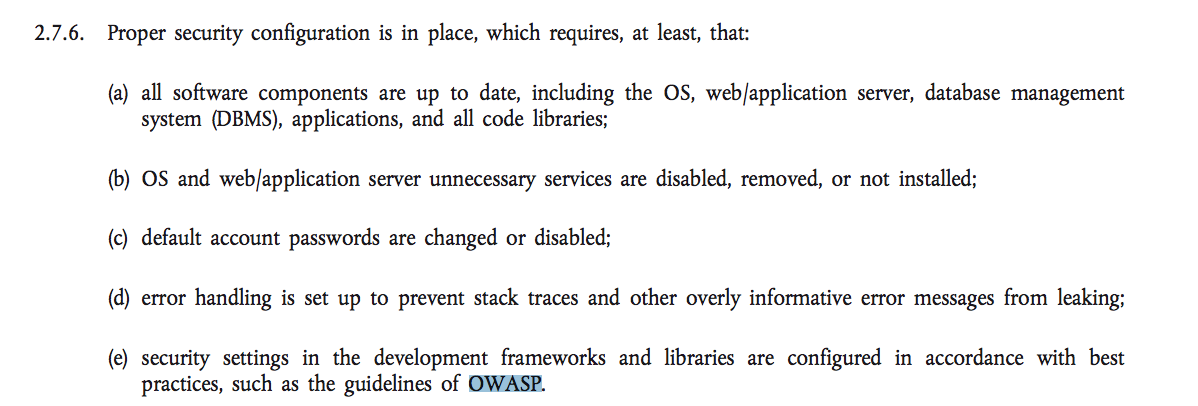
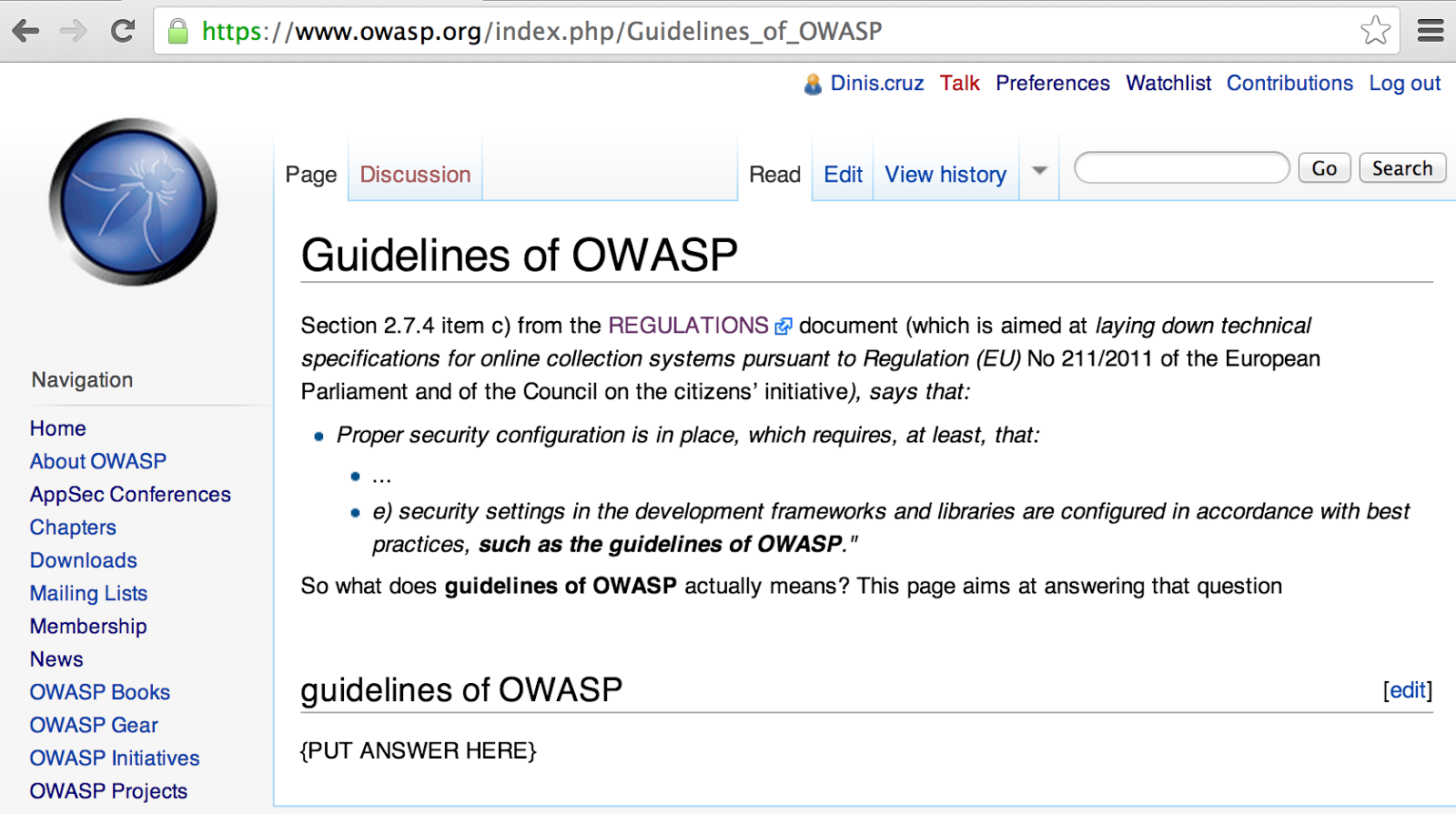
5.4 Guidelines of OWASP
OWASP got a great quote on this EU Regulations document which is aimed at laying down technical specifications for online collection systems pursuant to Regulation (EU) No 211/2011 of the European Parliament and of the Council on the citizens’ initiative)
Do a search for OWASP and you find 2 references, with the 2nd being this one:
This is great, but what are these ‘Guidelines of OWASP’?
Ideally we should should have a series for very explicit and focused ‘Guidelines’ to answer this question :)
To kickstart this process I created the Guidelines of OWASP page at the OWASP Wiki, so if you have some cycles, please chip in with your views:
5.5 Hack Yourself First: Jeremiah at TEDxMaui
Jeremiah was recently at TEDxMaui presenting Hack Yourself First which is an interesting development for WebAppSec and OWASP since I think it is the first time that a member of our community gets to present at TED (which is one of the best conference-series in the world)
Couple comments:
- he was quite nervous, which shows the ‘pressure to deliver’ that TED has.
- See Jeremiah’s Written Speech (i.e. what he wanted to say) and his personal comments about the experience)
- I really like the concept of ‘Hack yourself first’ but I wished Jeremiah had given more examples on how to do it an a personal, corporate and organisational level
- there was FAR too much FUD for my taste. I would had been better if he found a more positive way to deliver the message
- It is also quite obvious by Jeremiah performance that he really cares about WebAppSec and wants to make the world more secure
- Of course that he owns a company that helps companies to ‘Hack themselves first’ so there is a lot of vested interest in there too :)
- I think that OWASP doesn’t get one mention, which is not Jeremiah’s fault. I just shows the weakness of the OWASP Brand
Here is the Video:
5.6 I think the time as come for OWASP to have its own secure browser(s)
The idea is to create a customised version of a popular browser (like Chrome or Firefox) that has been customised to be secure out-of-the-box.
It could even be something like http://www.srware.net/ but I want to leverage the trust-network that OWASP has (and its potential to peer-review) to create a piece of software that I actually trust (or that it can earn my trust with time)
We should also add extensions that improve its security (after doing a security review on them).
This will not be an easy road since creating secure apps is very hard, but I think that doing this in a public forum (like OWASP) will help to sort out a lot of the current (workflow and technological) problems.
I finally reached this conclusion by being (again) in Starbucks with the potential of my blog being compromised
5.7 Nice list of 20 online coding tools
There is definitely a lot of innovation happening in this space, check out the list at The top 20 online coding tools from .Net magazine.
And if we want to enable the next generation of developers to code securely we need to integrate our knowledge into their IDEs (like these ones). Humm …. I wonder how hard it will be to add TeamMentor integration to these IDEs?
Note that this is on a mainstream developer magazine and (predictably) a search for ‘security’ or ‘owasp’ has 0 hits on that page:
5.8 No OWASP app on the OSX AppStore (Nov 2013)
Definitely a missed opportunity here :)
What types of App should exist?
At least we should have a couple that expose OWASP materials (books, wiki pages) , projects and events.
I will be a happy guy when this page doesn’t look like this:
5.9 OWASP and Privacy issues, we need to be involved
Following the original post of https://www.owasp.org/index.php/User_Privacy_Protection_Cheat_Sheet and an owasp-leaders thread on ‘OWASP should not have a political voice’, I wrote this:
Well we can’t ignore reality. That CS (CheatSheet) raises a lot of good points and provides very valuable information to devs who want to support their users that way.
I don’t think that the solution for OWASP is to curate the content based on political sensitives (since they vary around the world).
The solution is surely to present the multiple points of view (maybe even on different CS) and cross-link them. Why don’t we have a CS on ‘User Privacy protections accepted by governments” or “User Privacy for the user that has nothing to hide”
Privacy is very important topic , but due to trying to be ‘politically correct’ OWASP has failed to be involved. I’m glad this is starting to change, the politics are coming to WebAppSec so we need to accept that, and present technically correct analysis and guidance on ‘hot’ topics
And remember that the beauty of OWASP’s open and Wiki-driven model is that if you don’t like something, you can create a better one next door, and with time, the best one will gain the limelight/credibility/reputation (which is why ‘Reddit like threads’ are SO important for OWASP)
Edit: Here is a reddit page for this CheatSheet
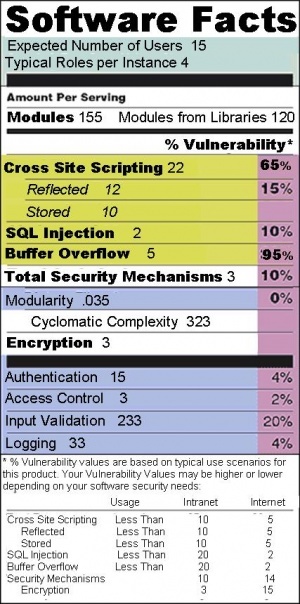
5.10 Software Labels – Jeff’s OWASP AppSecDC 2010 presentation (another dropped good idea)
An old idea from Jeff Williams (which is spot on) is the need to apply Labels to Software and Web Applications.
The concept is simple, but its implementation is really hard, because of the lack of quality standards/metrics in our industry
Here are Jeff presenting his idea two years ago: Don’t Judge a Website by its Icon - Read the Label!
This is a really important concept, and its complete lack of adoption (and traction) speaks volumes for our industry
For example, how am I supposed to make informed decisions as a software/website user if I cannot be exposed to something like this:
Also related is the idea o Idea for OWASP Standard for public rating of an WebSite’s security profile which could also create these useful labels: